Replies: 6 comments 2 replies
-
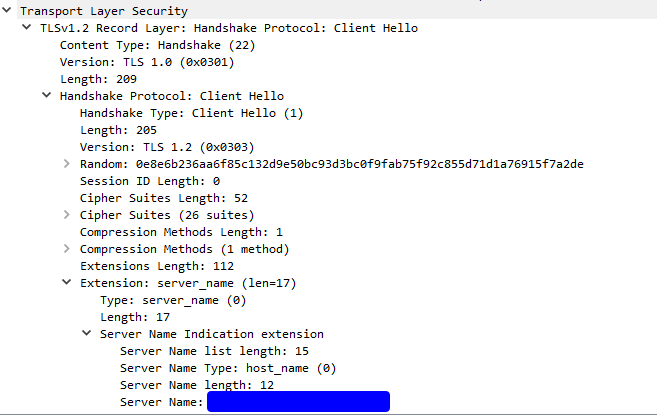
This means that the client is actively telling the proxy that it does not trust the certificate served by the proxy. Is the client sending a SNI? |
Beta Was this translation helpful? Give feedback.
-
|
As mentioned when visiting the IP via the browser I also get the message |
Beta Was this translation helpful? Give feedback.
-
|
I also ran mitmweb with the flags |
Beta Was this translation helpful? Give feedback.
-
|
If there is a server name indication, mitmproxy should generally be able to generate a trustworthy certificate (assuming its CA is trusted).
Does not really matter, that would be a
|
Beta Was this translation helpful? Give feedback.
-
|
Okay, thanks for taking the time to look into it . Don't know where exactly to continue, but I will have a closer look at the setup and report back if I find anything 👍 |
Beta Was this translation helpful? Give feedback.
-
|
CA cert must be trusted by client (also ensure it is the right initially generated CA cert), see #5307 (comment). |
Beta Was this translation helpful? Give feedback.
-
Hey!
I have a problem with sniffing the traffic of a mobile application.
The mitmproxy certificate is installed and working well when connecting to https sites via the browser.
Also SSL pinning doesn't seem to be a problem, because I can see the traffic when running it on a different setup with mitmproxy in regular mode.
When running it on another setup where I use transparent mode (I think this shouldn't make a difference) I can see SOME of the https traffic, but for a certain domain I am spammed with the following error:
When visiting
Y.Y.Y.216(IP redacted) I can see, that the certificate is indeed not valid.Even if I enable the option
ssl_insecureI get the same error.Do you have an idea what else I can try?
My setup:
Beta Was this translation helpful? Give feedback.
All reactions