You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
The products and vendors, which are listed in the affected Column of a CVE are often not vulnerable.
For example:
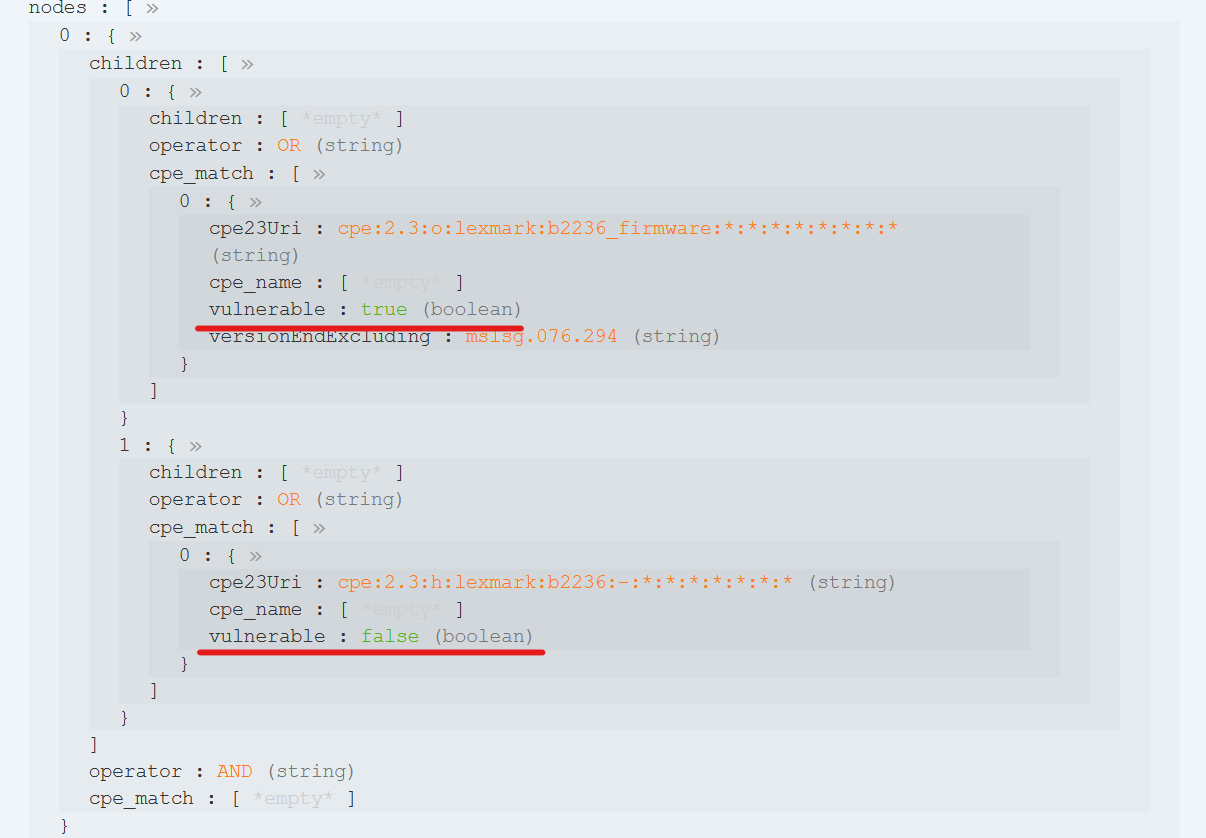
The CVE-2021-44738 has multiple configurations, but only one of each configuration is vulnerable.
From the first configuration only "b2236_firmware" is vulnerable, but not "b2236", if you check the JSON object.
The solution would be to change the function convert_cve in opencve/utils.py.
Instead of just using the nested_lookup for the cpe23Uri, there could be a if-statement, checking if the boolean for vulnerable is True.
If there is a intend, that, for example the OS or the hardware is listed as affected in a CVE, then there could be another possibility to differentiate between associated and vulnerable products. The problem without distinction is, that, via the mail-service, the users gets a lot of notifications, which are not relevant, if he/she doesn't have the actual vulnerable software installed.
PS. big fan of this project, keep the good work up 😄
The text was updated successfully, but these errors were encountered:
The products and vendors, which are listed in the affected Column of a CVE are often not vulnerable.
For example:
The CVE-2021-44738 has multiple configurations, but only one of each configuration is vulnerable.
From the first configuration only "b2236_firmware" is vulnerable, but not "b2236", if you check the JSON object.
The solution would be to change the function convert_cve in opencve/utils.py.
Instead of just using the nested_lookup for the cpe23Uri, there could be a if-statement, checking if the boolean for vulnerable is True.
If there is a intend, that, for example the OS or the hardware is listed as affected in a CVE, then there could be another possibility to differentiate between associated and vulnerable products. The problem without distinction is, that, via the mail-service, the users gets a lot of notifications, which are not relevant, if he/she doesn't have the actual vulnerable software installed.
PS. big fan of this project, keep the good work up 😄
The text was updated successfully, but these errors were encountered: