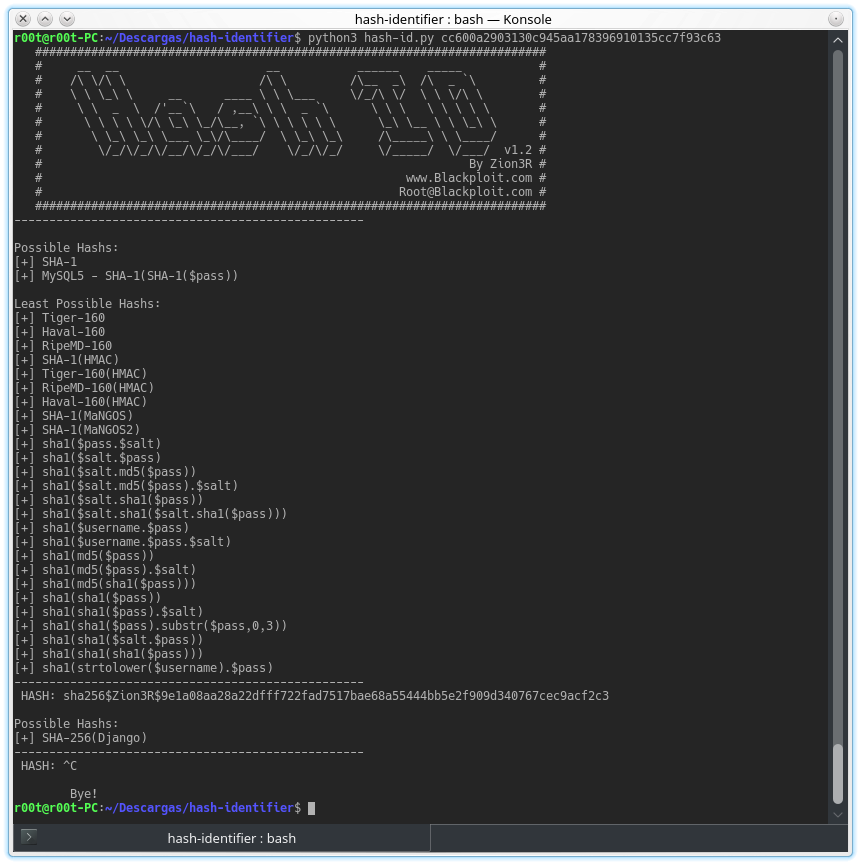
Software to identify the different types of hashes used to encrypt data and especially passwords.
Encryption formats supported:
- ADLER-32
- CRC-32
- CRC-32B
- CRC-16
- CRC-16-CCITT
- DES(Unix)
- FCS-16
- GHash-32-3
- GHash-32-5
- GOST R 34.11-94
- Haval-160
- Haval-192 110080 ,Haval-224 114080 ,Haval-256
- Lineage II C4
- Domain Cached Credentials
- XOR-32
- MD5(Half)
- MD5(Middle)
- MySQL
- MD5(phpBB3)
- MD5(Unix)
- MD5(Wordpress)
- MD5(APR)
- Haval-128
- MD2
- MD4
- MD5
- MD5(HMAC(Wordpress))
- NTLM
- RAdmin v2.x
- RipeMD-128
- SNEFRU-128
- Tiger-128
- MySQL5 - SHA-1(SHA-1($pass))
- MySQL 160bit - SHA-1(SHA-1($pass))
- RipeMD-160
- SHA-1
- SHA-1(MaNGOS)
- Tiger-160
- Tiger-192
- md5($pass.$salt) - Joomla
- SHA-1(Django)
- SHA-224
- RipeMD-256
- SNEFRU-256
- md5($pass.$salt) - Joomla
- SAM - (LM_hash:NT_hash)
- SHA-256(Django)
- RipeMD-320
- SHA-384
- SHA-256
- SHA-384(Django)
- SHA-512
- Whirlpool
- And more…
Encryption algorithms that can not be differentiated unless they have been decrypted, so the efficiency of the software also depends on the user's criteria.